Digital technology is reshaping business models, revenue streams and operations management. At the same time, the rising number of start-ups, scale-ups and unicorns in Europe — the digital-native businesses — is helping to boost digital transformation (DX) initiatives in traditional organisations.
What Is a Digital-Native Business?
Digital-native businesses (DNBs) are highly dependent on a digital infrastructure and are built from the start around modern technologies, from cloud-native applications to artificial intelligence, with data across all aspects, from operations to business models and customer engagement. By adopting new and emerging technologies, and using platform services and marketplaces, DNBs can quickly grow and scale up their business, creating new markets and disrupting traditional business models across industries.
DNBs are also defined by their market valuation — start-ups are valued at less than $250 million, scale-ups are valued from $250 million to $999 million and mature digital natives are valued at $1 billion or more. They can also be either technology-orientated companies (e.g., innovative ISVs/SaaS providers, selling technology products, software or IT services to other businesses) or technology-driven B2B or B2C companies (offering tech-enabled products or services respectively to business or consumers).
What Impact do DNBs have on Traditional Enterprises?
DNBs are disrupting some industries more than others. Fintech companies such as Revolut in the UK and digital banks such as N26 in Germany have pushed digital innovation in the past few years into a very traditional sector, whereas Sweden-based Spotify has completely reshaped the music industry at a global level.
DNBs’ influence also extends to the way traditional companies adopt and use technology. DNBs’ tech operations are often cloud native and data driven, with a customer-centric focus, employing tech-savvy developers and data scientist teams in agile environments to grow and scale the business quickly.
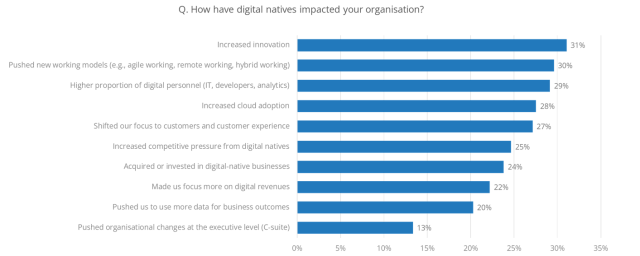
Market disruption and the growing interaction with DNBs are driving traditional European organisations to adopt some of the DNBs’ distinguishing digital features, such as shifting towards a digital-first organisational approach across the enterprise. According to IDC’s What Is the Impact of Digital-Native Businesses on Traditional Enterprises? — based on IDC’s 2022 European Industry Acceleration Survey — these impacts include:
- Increased innovation: 35% of businesses with more than 1,000 employees cited this. Healthcare (37%), government/education (34%) and transport (34%) are the most impacted industries. Healthtech, edtech and the shared economy are the fastest-growing segments in the DNB arena.
- Adoption of new working models: The implementation of agile, remote and hybrid ways of working pushed by the interaction with DNBs is most common in very large enterprises, government, education, and retail and wholesale industries. These extensively adopted remote working during the pandemic, and are now taking inspiration from DNBs to permanently adopt new and flexible working models.
- Higher proportion of digital personnel: Finance respondents have increased the share of employees with digital skills (38%), and have a greater focus on customers and CX (31%), a trend influenced by the interrelationship with the fintech ecosystem. On a broader level, medium, large and very large organisations also say DNBs have had a major impact on organisational changes at the C-suite level.
Why Is it Important to Monitor the Relationship Between Digital Natives and Traditional Businesses?
IDC’s European Industry Acceleration Survey highlights growing coopetition between DNBs and traditional organisations. This is leading to a more innovative and digital-first organisational approach for the latter, such as a tighter focus on digital revenues, across all size categories, and greater competitive pressure in their respective markets, which may enable them to enter M&As or investment activities with DNBs.
This last trend is more prominent for utilities and oil/gas respondents, an industry where customer-orientated digital natives have pushed traditional companies towards improving their CX, also by acquiring entirely digital organisations in the process and with new market segments (such as renewables) being led by digital-native businesses.
Tech providers should target European DNBs, as this is a competitive, fast-growing segment populated by lean, agile and tech-enabled organisations. DNBs are built around modern technologies and digital infrastructure, and need to enter strategic partnerships with external stakeholders to meet their need for innovation. Tech providers are the first option for European DNBs, according to preliminary results from IDC’s Global Digital-Native Business Study.
Tech providers should also look to DNBs as precursors of the changes and trends that will affect traditional industries. Changes range from greater adoption of cloud services (cited especially by telecommunications and media, finance, and professional services respondents) to the adoption of a data-driven approach to business outcomes (cited by 19% of very large enterprises and 25% of retail/wholesale respondents). What DNBs need today will be what traditional businesses need tomorrow.
The relationship between DNBs and traditional organisations could span from tech supplier to potential acquisition target. This could change based on their business model, giving birth to interconnected ecosystems. For these reasons, in cultivating a long-term relationship with digital natives, tech vendors can also improve their positioning in traditional enterprises as trusted partners in their DX journeys.
To find out more about digital-native businesses in Europe, please contact Martina Longo.